On 25.09.2014 a severe internet security alert was issued for many Linux/Mac systems. stSoftware immediately patched all our cloud hosted servers in response to this alert.
We advise individuals or organisations with Unix-based systems they will need to patch all internet facing Linux/Mac servers immediately.
See Severe Bash vulnerability affects Unix-based systems including Linux and Mac OSX for more information on how to manage this internet security issue.
We recommend internet users subscribe
- 26 Sep 2014
Overview
The Heartbleed Bug is a recently discovered vulnerability in the OpenSSL cryptographic software library used by many of the world’s web servers to secure information using TLS. If the web site is vulnerable then a hacker could expose 64k of the server's memory without any trace in the server's logs. The server's memory exposed could include the server's private encryption key or other information such as usernames and passwords.
- 11 Apr 2014
Overview
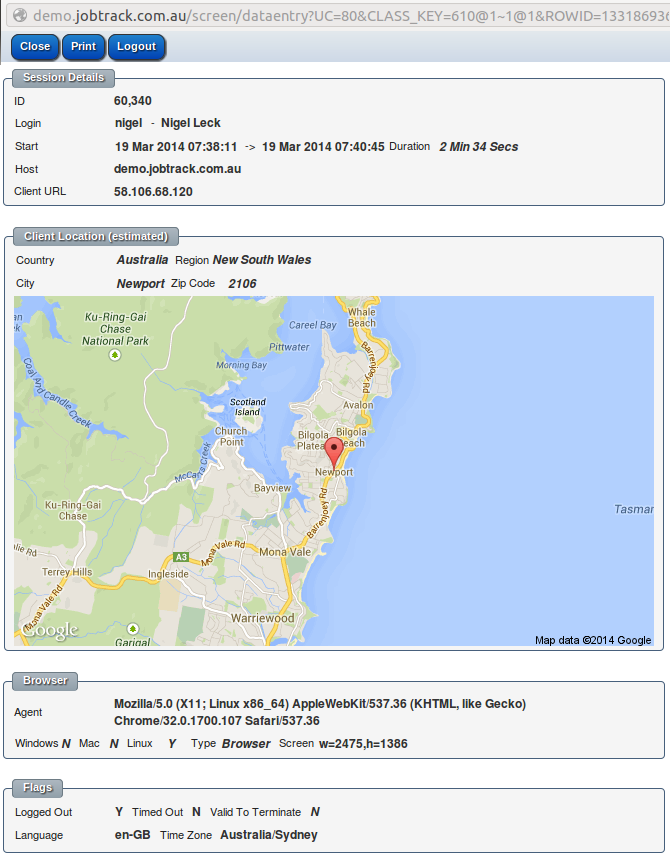
Normal users are restricted to view only their own session details. Administrators may see the session details for all users.
Active sessions can be forcibly logged out from the session details screen. The list of active sessions for a user can be viewed from the "My Setup" screen.
- 8 Apr 2014
Security
Industry standard best practice for passwords for both the web server and Linux machines. Site designers do not have direct access to the underlying Linux server, the raw database or files. All changes are done within sandbox of the system.
- 26 Nov 2013
The file /etc/hosts.deny on Unix/Linux can block login attempts based on counties. The below is a simple host.deny file to block all countries but your own ( in my case Australia), sure this is not the whole answer to securing a system but it sure cuts down the number of hack attempts.
sudo vi /etc/hosts.allow
#
# hosts.deny This file describes the names of the hosts which are
# *not* allowed to use the local INET services, as decided
# by the '/usr/sbin/tcpd' server.
#
# We will block *all*
- 25 Jul 2013